Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
585 Results Found
411 - 420 of 585 results
Published on 05.06.2020
CIS Benchmarks End of Life for Unsupported TechnologiesIn addition to being costly and troublesome, the continued use of unsupported technologies can expose your organization to security risks. Patchi...
Published on 04.30.2020
CIS Controls Volunteer Spotlight: Giacomo LunardonThe CIS Controls offer prioritized and prescriptive guidance on how to achieve an effective cybersecurity program. They are developed through a c...
Published on 04.28.2020
Automating the Generation of Windows Vulnerability Detection ContentWith a plethora of cybersecurity threats on the horizon, it’s important that professionals have a common language for discussion and analysis. Op...
Published on 04.20.2020
Resource Guide for Cybersecurity During the COVID-19 PandemicAccording to the results of the CSO Pandemic Impact Survey, 61% of the security and IT leader respondents are concerned about an increase in cybe...
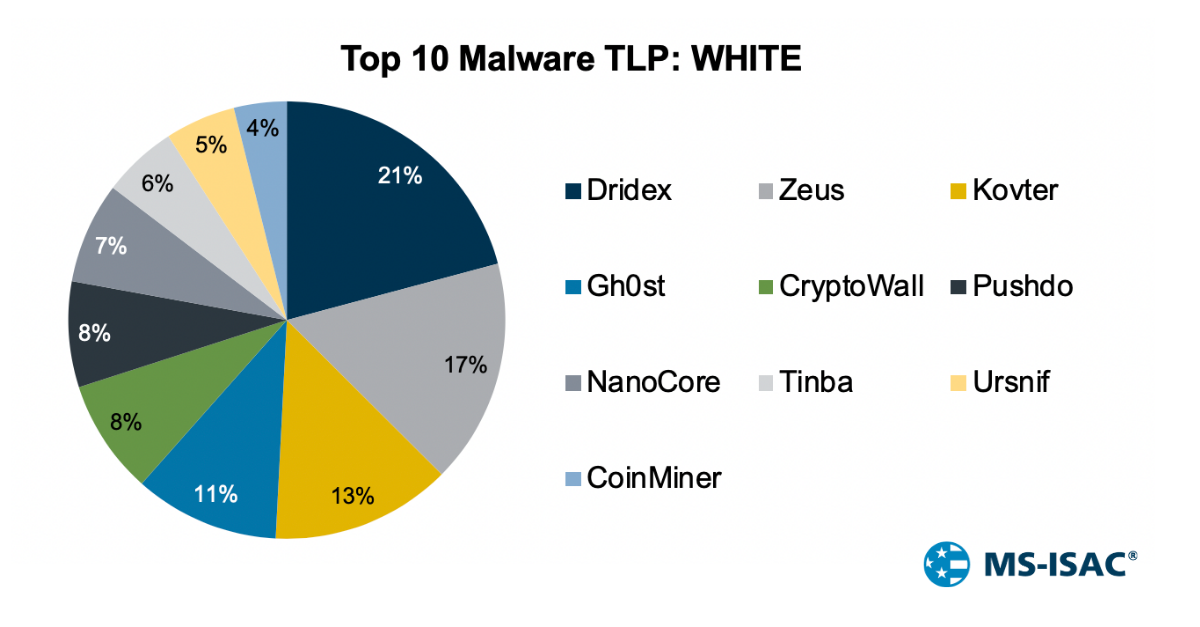
Published on 04.16.2020
Top 10 Malware March 2020Top 10 Malware composition was fairly consistent with February 2020 with the exception of Pushdo and Tinba. Overall, the Top 10 Malware variants ...
Published on 04.07.2020
Cybersecurity Challenges of a Sudden Remote WorkforceIT teams have spent recent weeks enabling staff at their organizations to work from home. Unexpected cybersecurity challenges are arising related...
Published on 04.03.2020
6 Educational Cybersecurity Resources for KidsKids and teens around the country are staying home and adapting to a new virtual school environment. While the adjustment is fun for a while, the...
Published on 03.30.2020
CIS Hardened Images Built on Google Cloud’s Shielded VMsGoogle Cloud announced general availability of its Shielded VMs (virtual machines) at a breakout session during Google Cloud Next ‘19. As a resul...
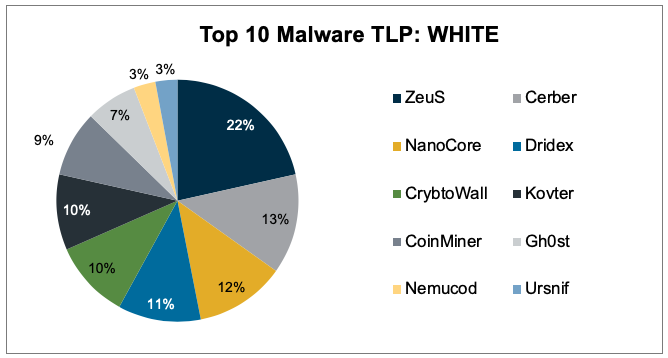
Published on 03.24.2020
Top 10 Malware February 2020Top 10 Malware composition is very consistent with January 2020 with the exception of Ursnif. Nemucod remained, for the second month in a row, in...
Published on 03.19.2020
How CIS Can Help Teleworkers Improve their Cyber DefensesAs the COVID-19 pandemic is forcing more and more companies to adjust their work schedules and move to telework environments, CIS remains committ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More