Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
655 Results Found
Solutions
Industry
521 - 530 of 655 results
Published on 09.17.2019
By Sean Atkinson, Chief Information Security Officer When we think of a sector or industry most prone to cybercriminal activity, the financial se...
CIS BenchmarksCIS SecureSuiteFinance
Published on 09.10.2019
By Sean Atkinson, Chief Information Security Officer & Stephanie Gass, Information Security Audit and Governance The 80s and 90s may have been th...
CIS Controls
Published on 09.03.2019
While some identity management protocols such as multi-factor authentication have made modern advancements, others – like email authentication – ...
Published on 08.28.2019
Telecommuting is more popular than ever, allowing people to work from home or alternative environments away from the traditional office. Accordin...
CIS Controls
Published on 08.27.2019
CIS and PCI SSC work together on an ongoing basis to increase payment data security everywhere. Here's a look at how.
CIS BenchmarksCIS SecureSuite
Published on 08.15.2019
Whether your organization operates on-prem or in the cloud, cybersecurity should be your top priority. Easier said than done, right? Operating sy...
CIS BenchmarksCIS Hardened Images
Published on 08.13.2019
Secure configurations are a key best practice for limiting your organization’s cyber vulnerabilities. Because systems don’t ship securely, it’s i...
CIS BenchmarksCIS SecureSuite
Published on 08.06.2019
Being an Information Security Senior Auditor brings different challenges every day. Whether she’s helping conduct assessments or evaluating risk ...
CIS Controls
Published on 07.31.2019
When data is the lifeblood of your organization, ransomware hits like a heart attack. Are you prepared? Ransomware is a type of malware that bloc...
CIS Controls
Published on 07.10.2019
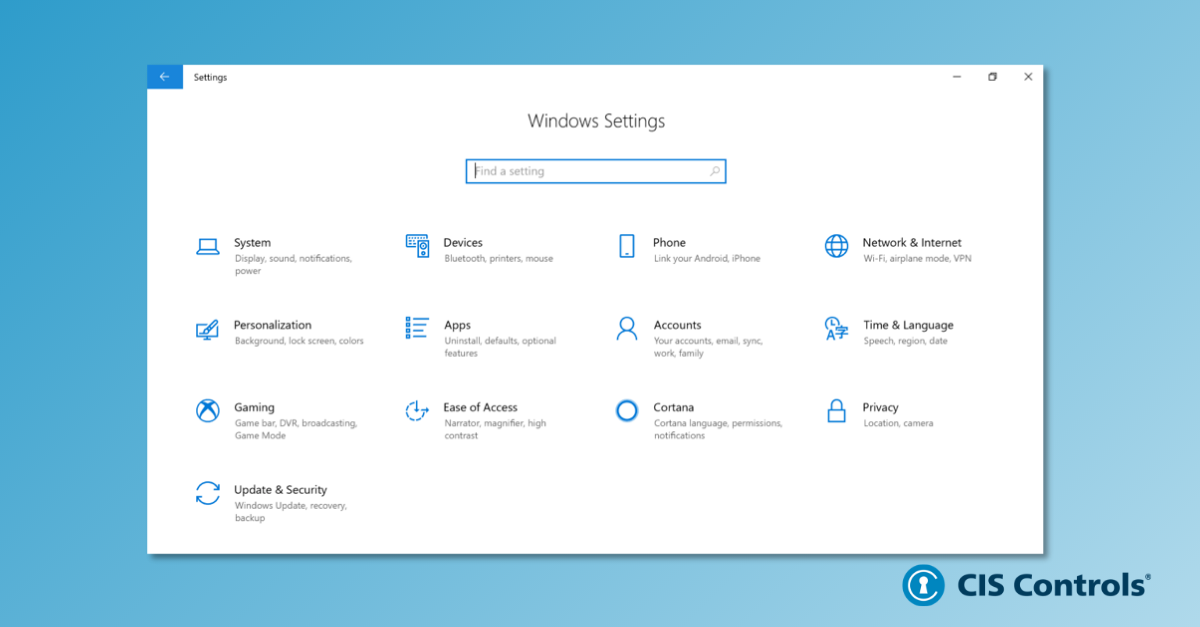
According to both Net Applications and Stat Counter, all versions of the Microsoft Windows operating systems combined represent well over 50% of ...
CIS Controls
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More