Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
585 Results Found
501 - 510 of 585 results
Published on 10.11.2018
11 of the Coolest Technical Jobs at CISThere are hundreds of different technical jobs in the cybersecurity industry, with millions of unfilled positions around the globe. Each position...
Published on 10.09.2018
Cybersecurity Career Q&A with CIS’ CISOTo celebrate this week’s theme of ‘Educating for a Career in Cybersecurity’ during Cybersecurity Awareness Month (CSAM), we wanted to get an insi...
Published on 10.04.2018
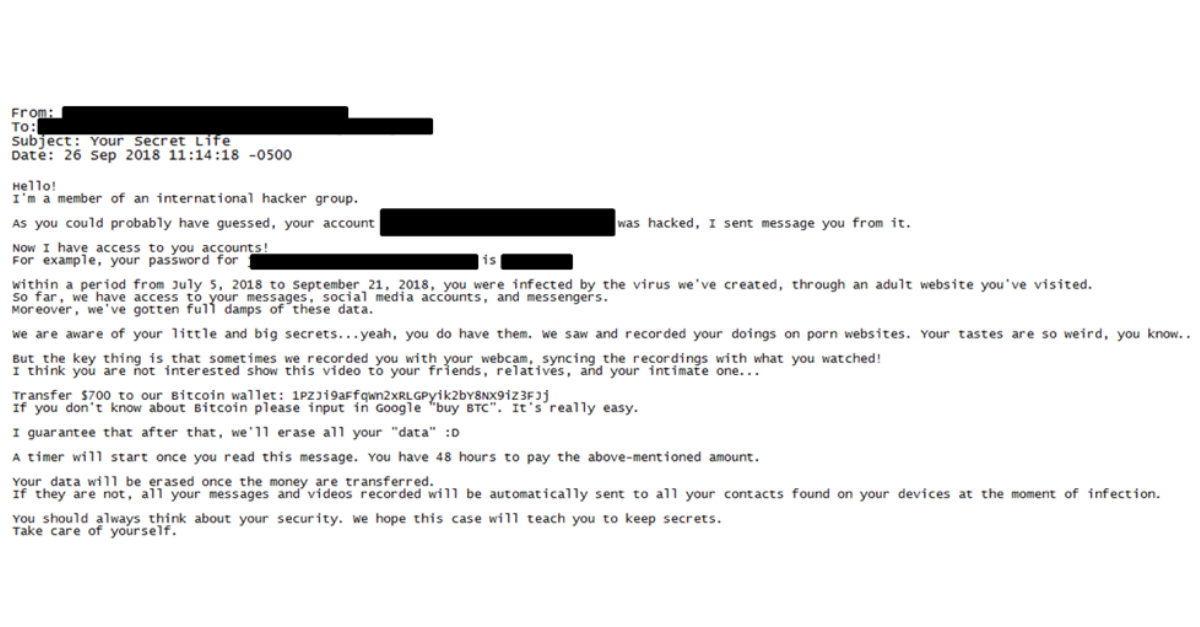
Sextortion Hoax Scams Continue with Updated TacticsSextortion hoax scams continue to affect state, local, tribal, and territorial (SLTT) government employees, who are reporting updated email tacti...
Published on 10.02.2018
How 4 of the CIS Controls Can Help Secure Your Home NetworkFacing everything from viruses to malware, home and personal networks can be just as vulnerable to cyber crime as organizational systems. We spok...
Published on 09.27.2018
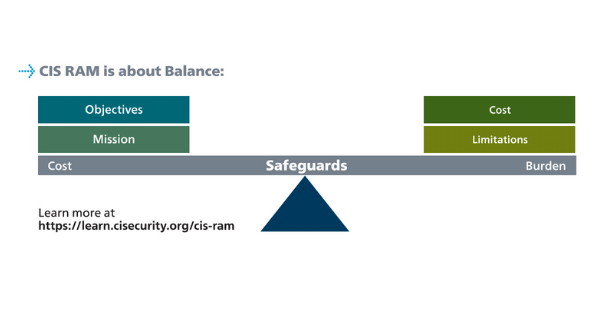
60 Minutes to a Better Risk Assessment Outcome with CIS RAMWant to know more about risk analysis? Check out the presentation below by Chris Cronin, a partner at Halock Security Labs and Chair of the DoCRA...
Published on 09.25.2018
CIS Benchmarks Volunteer Spotlight: Nancy Hidy WilsonMore than 9,000 members of the CIS Benchmarks™ Community have developed and updated CIS Benchmarks for over 150 technologies. Our latest communit...
Published on 09.20.2018
The Chaos ExperimentBy Sean Atkinson, Chief Information Security Officer Progression through development operation methods means introducing new elements that are as...
Published on 09.18.2018
DevSecOps – An Integrated Approach to Coding SecurityBy Sean Atkinson, Chief Information Security Officer As the world requires more code, more applications, more interfaces, and more digital servic...
Published on 09.11.2018
Albert: A Smart Solution for Network MonitoringThe world of network monitoring can seem a bit intimidating at first. There are a variety of solutions on the market offering to detect, alert, a...
Published on 09.04.2018
CIS RAM and Use with Regulatory FrameworksBy Chris Cronin, Partner, HALOCK Security Labs CIS RAM is an information security risk assessment method that helps organizations conduct cyber r...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More