Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
585 Results Found
281 - 290 of 585 results
Published on 09.17.2021
The Role of Service Providers in Transforming SecurityBy: Kathleen M. Moriarty, CIS Chief Technology Officer Cyber-attacks are increasing in severity. Cybercriminals now use the supply chain, managem...
Published on 09.09.2021
Join CIS at AWS Public Sector Summit 2021 in DCThe Center for Internet Security (CIS) is excited to sponsor and attend the Amazon Web Services (AWS) Public Sector Summit at booth 209. This yea...
Published on 09.07.2021
CIS Controls v8 Internet of Things & Mobile Companion GuidesThe Center for Internet Security (CIS) launched CIS Controls v8 earlier this year. It was enhanced to keep up with evolving technology (modern sy...
Published on 09.07.2021
Four Reasons to Use Hardened VMs for Your Cloud MigrationEnsuring your organization’s IT environment is not only secure, but also patched regularly, can be challenging. Migrating to the cloud can help a...
Published on 08.27.2021
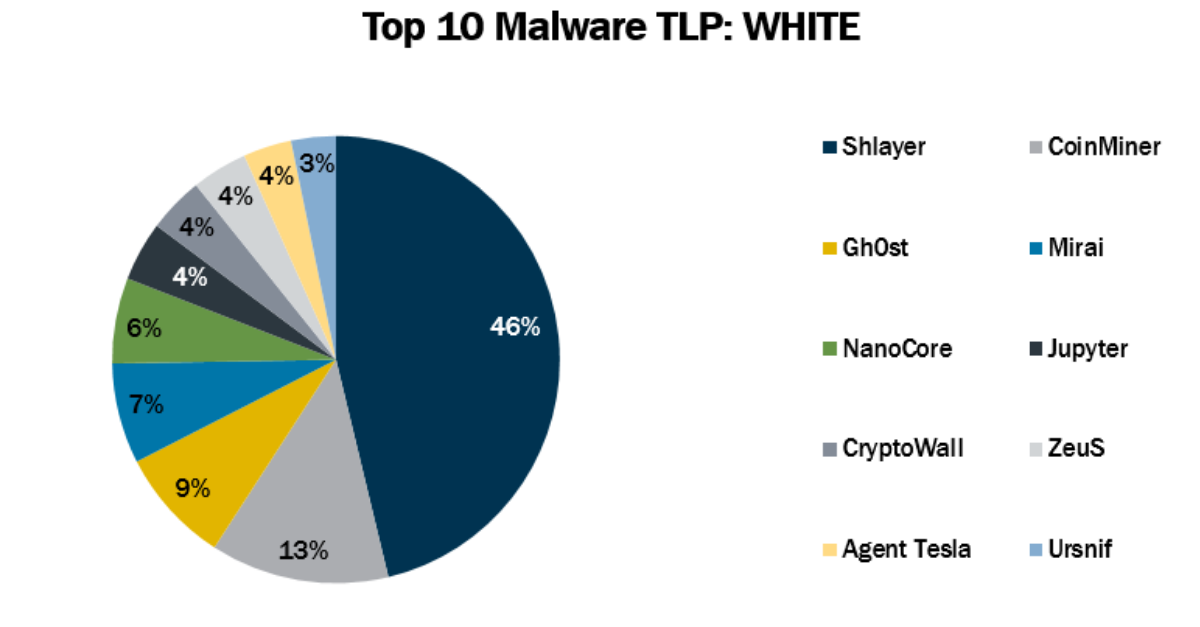
Top 10 Malware July 2021In July 2021, the MS-ISAC observed Agent Tesla and Jupyter’s return to the Top 10. The Top 10 Malware variants comprise 63% of the total malware ...
Published on 08.26.2021
How to Identify an Email Hoax & What to do if You Fall VictimEmail hoaxes demand money by threatening recipients in various ways. The sender may claim that they will unleash a distributed denial of service ...
Published on 08.18.2021
How to Layer Secure Docker Containers with Hardened ImagesAs organizations utilizing the cloud mature, they find more innovative and effective solutions for their workloads. Containerized applications of...
Published on 08.12.2021
How to Meet STIG Compliance and Achieve OS Security with CISOrganizations tasked with meeting regulatory framework compliance know the difficulties they will face. On top of the resource hours, it can be c...
Published on 08.05.2021
CIS Benchmarks August 2021 UpdateCIS Ubuntu Linux 20.04 LTS STIG Benchmark v1.0.0 This Benchmark offers prescriptive guidance for establishing a secure configuration posture for ...
Published on 07.29.2021
The Mirai Botnet – Threats and MitigationsCreated by Josiah White, Paras Jha, and Dalton Norman, the Mirai botnet was initially written in C for the bots and Go for the controllers, with ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More