Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
585 Results Found
231 - 240 of 585 results
Published on 02.24.2022
How Configuration Assessments Help Improve Cyber DefensesThere's an old adage in business; if you're not measuring something, you can't manage it. These days, information technology (IT) and information...
Published on 02.22.2022
Top 10 Malware January 2022In January 2022, the Top 10 stayed consistent with the previous month except Snugy returned to the Top 10, while CryptoLocker made its first appe...
Published on 02.16.2022
Assess, Remediate, and Implement with CIS SecureSuiteThe world relies on technology. So, a strong cybersecurity program is more important than ever. The challenge of achieving good cyber hygiene can...
Published on 02.02.2022
The Cost of Ignoring the Log4j VulnerabilityIgnorance is not bliss when it comes to the Log4j vulnerability. In the past month, organizations have been scrambling to understand their exposu...
Published on 02.02.2022
CIS Benchmarks February 2022 UpdateThe CIS Benchmarks team has recently made updates the CIS SUSE Linux Enterprise Benchmark.
Published on 01.28.2022
Jupyter: A Cyberspace Invader Stealing SLTT DataThe Multi-State Information Sharing and Analysis Center (MS-ISAC) Cyber Threat Intelligence Team (CTI) assesses with moderate confidence that Jup...
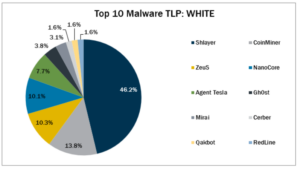
Published on 01.28.2022
Top 10 Malware December 2021For December 2021 Cerber, RedLine, and Qakbot. Cerber and Qakbot returned to the Top 10, while RedLine made its first appearance.
Published on 01.27.2022
Protecting Privacy Using the CIS Controls Privacy GuideThe CIS Controls Privacy Guide provides best practices and guidance for implementing the CIS Critical Security Controls (CIS Controls) while cons...
Published on 01.27.2022
2022 Cybersecurity Predictions to Watch Out ForAs eventful as 2020 was, 2021 was equal to its predecessor. It was a year that bounced from hope to cautious optimism, then back to disquiet. Whi...
Published on 01.20.2022
CIS Risk Assessment Method (RAM) v2.1 for Implementation Group 2 (IG2)CIS Risk Assessment Method v2.1 for IG2 is designed to help justify investments for reasonable implementation of the CIS Critical Security Contro...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More