Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
582 Results Found
261 - 270 of 582 results
Published on 10.21.2021
Guest Podcast: Why is Security Recruiting so Broken?Cybersecurity recruiting challenges: is there truly a lack of applicants, or are employers looking in the wrong places? CIS Senior Vice President...
Published on 10.21.2021
NGINX + CIS Hardened Images = Security at Top EfficiencyJust under 25% of the internet’s busiest websites – including Dropbox, Netflix, and WordPress.com – served or proxied NGNIX in July 2021, accordi...
Published on 10.20.2021
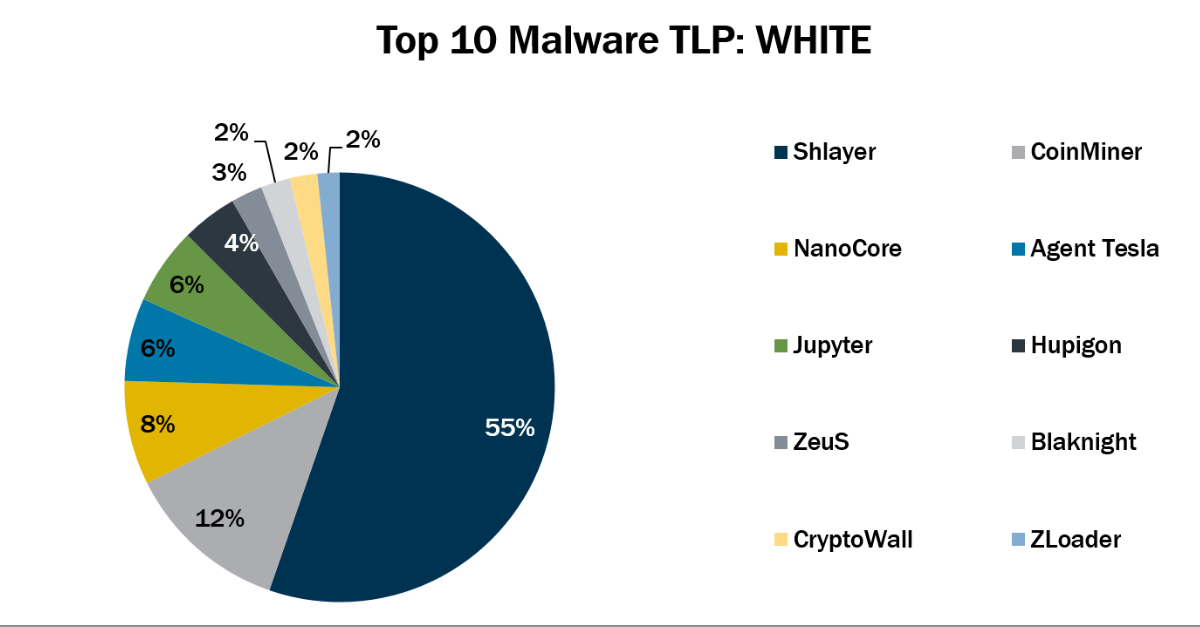
Top 10 Malware September 2021In September 2021, the MS-ISAC observed Jupyter’s return to the Top 10 Malware list. Additionally, ZLoader made its first appearance in the Top 1...
Published on 10.18.2021
Why Are Authentication and Authorization So Difficult?By: Kathleen M. Moriarty, CIS Chief Technology Officer Let’s say you’re tasked with selecting a strong authentication solution for your organizat...
Published on 10.15.2021
Enabling the Cooperative Cybersecurity EcosystemBy Adam Montville The Center for Internet Security (CIS) has a mission to improve the actual practice of cyber defense, and we do this, in part, ...
Published on 10.14.2021
Join CIS and MS-ISAC at Virtual 11th Annual Cyber Security SummitThe Center for Internet Security (CIS) and the Multi-State Sharing and Analysis Center (MS-ISAC) are proudly serving as partners for the Virtual ...
Published on 10.13.2021
Announcing CIS Endpoint Security Services for SLTTsU.S. State, Local, Tribal, and Territorial (SLTT) organizations face a stark challenge in mounting a proper cybersecurity defense against malicio...
Published on 10.07.2021
What’s in a Name? CIS Critical Security ControlsBy Tony Sager, CIS Sr. Vice President and Chief Evangelist The conversation that eventually led to the CIS Critical Security Controls started wit...
Published on 10.06.2021
Enter the Ransomware Arena, Live the Experience, and Discover How You Will React!Contingency plans in cybersecurity are essential when preparing for any incident, whether it is malware infecting an end user’s hard drive or ran...
Published on 10.06.2021
3 Ways to Use CIS Cloud Security Resources on the AWS CloudIt’s obvious that the remote capabilities of the modern day office have transformed permanently. Most organizations will see an increase in hybri...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More