All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter by Topic
1152 Results Found
1031 - 1040 of 1152 results
Published on 05.03.2018
GDPR – Are you ready?New regulations like GDPR (General Data Protection Regulation) can always be a bit intimidating – but they don’t have to be! If your organization...
Published on 05.02.2018
A Midwest Electric Utility uses CIS Controls as their Cybersecurity FoundationPublished on 05.01.2018
CIS Controls Inspire Law GraduateLearn about Jamal Hartenstein, who has combined his two passions - cybersecurity and the law - into a specialized law practice.
Published on 05.01.2018
Fault Trees and Risk ForestsBy Sean Atkinson, Chief Information Security Officer Risk management and the elicitation of scenarios Over the past few blog posts I have discuss...
Published on 04.30.2018
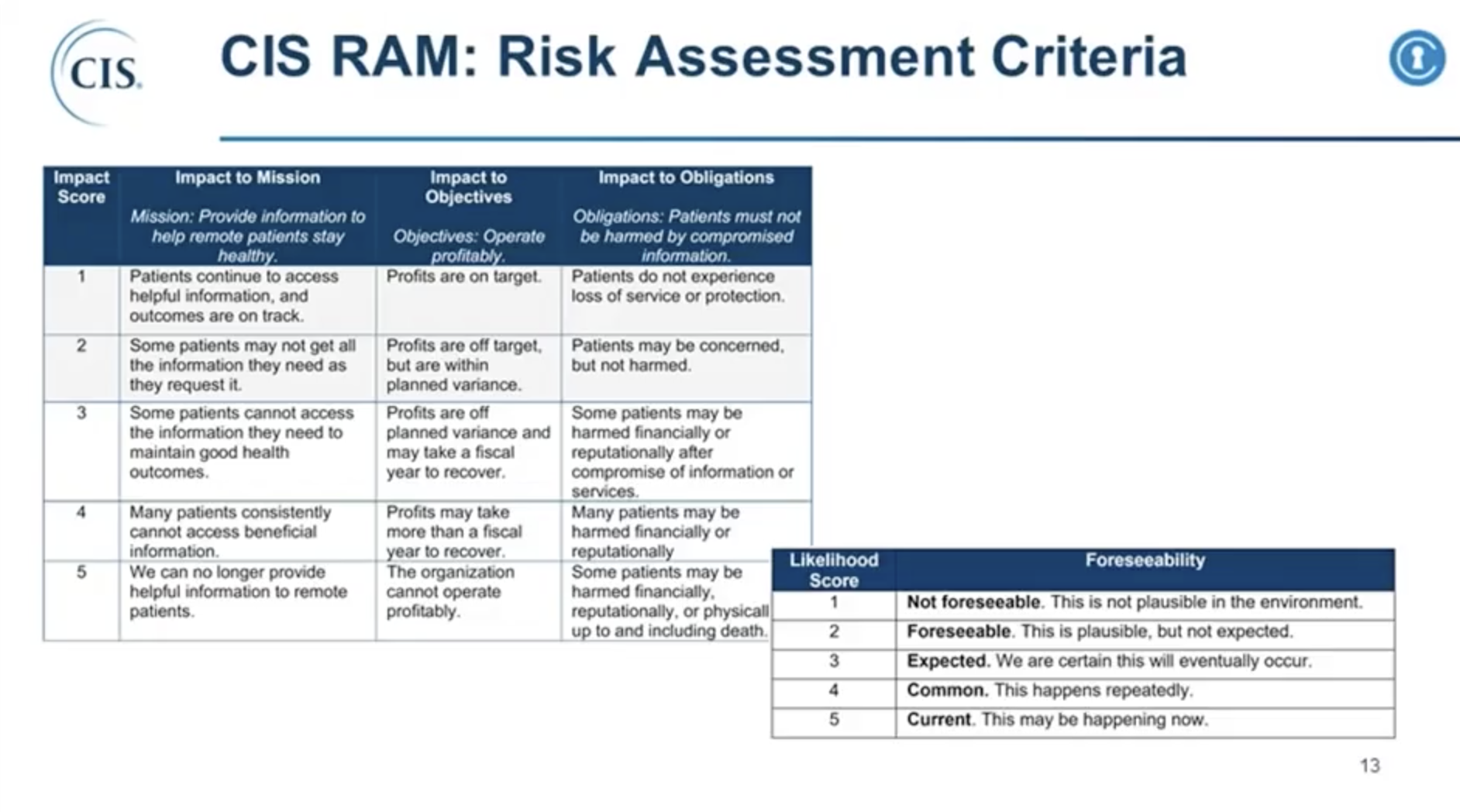
CIS RAM v1.0 (Risk Assessment Method) Launch EventApril 30, 2018 CIS RAM v1.0 (Center for Internet Security® Risk Assessment Method) is an information security risk assessment method that helps o...
Published on 04.27.2018
Election Security Spotlight – CIA TriadWhat it is The CIA Triad is a benchmark model in information security designed to govern and evaluate how an organization handles data when it is...
Published on 04.24.2018
Cloud Compliance – How to Stay Secure on an Intangible InfrastructureBy Sean Atkinson, Chief Information Security Officer “If it is not my device, how do I control it?” Security in the cloud can be a contentious to...
Published on 04.23.2018
MS-ISAC Security Primer – Exposed CredentialsOverview The impact of publicly exposed user credentials has far reaching affects, because credential reuse can result in data breaches, system c...
Published on 04.21.2018
Wilmington Gastroenterology uses the CIS Controls as a Foundation for Securing their PracticeLearn how one practice now relies on the CIS Controls as their security guideline and foundation for securing their environment.
Published on 04.20.2018
Election Security Spotlight – Cyber Kill Chain®What it is Earlier this week, US-CERT released a Joint Technical Alert (TA18-106A) detailing state-sponsored Russian cyber activity targeting pri...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More