Albert FAQ
Overview
What is Albert Network Monitoring and Management?
The Center for Internet Security (CIS) offers network security monitoring and management services through a solution referred to as Albert. This service is available to U.S. State, Local, Tribal, and Territorial governments, including elections, public education, and critical infrastructure entities. Albert can be used to monitor many types of traffic including networks with user workstations, web servers, or those hosting voter registration databases.
What environments does Albert work within?
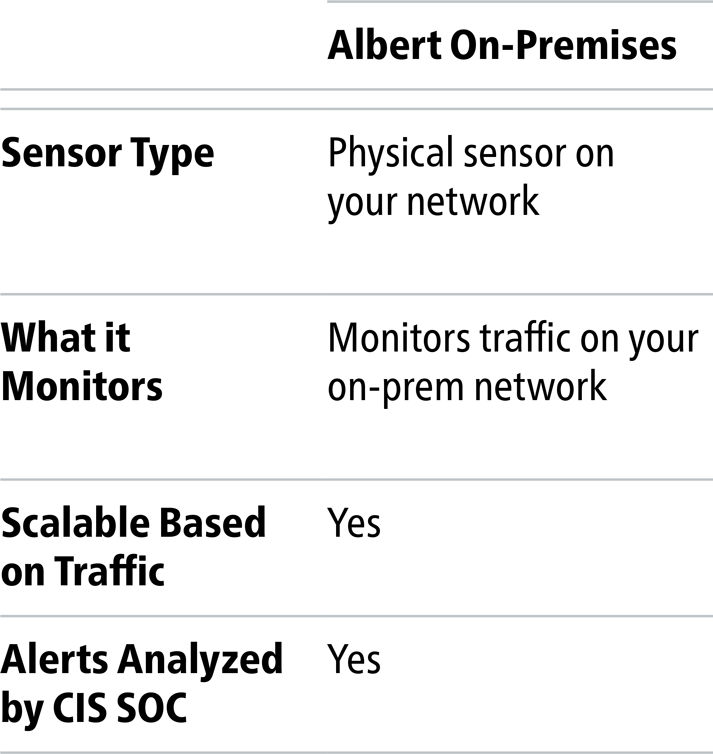
Albert Network Monitoring and Management is available for on-premises environments.
How does Albert work?
Albert is an intrusion detection system (IDS) based on open-source technology with a particular focus on threats to SLTT/election community organizations. Albert sensors monitor network traffic, to look for matches against a set of “signatures” that indicate the network traffic contains known cyber threats. Albert does not interfere or change the network traffic in any way and cannot inspect the contents of encrypted communications. The process proceeds as follows:
- An organization that hosts an Albert sensor selects the network segments to be monitored by the Albert sensor and configures their network to send a copy of the selected network traffic to the Albert Intrusion Detection System (IDS) sensor for inspection using what is called a “mirror port” or “network tap.” This parallel configuration means that normal network traffic and speeds are unaffected by Albert.
- CIS deploys (~25,000) daily threat “signatures” based on current cyber threat intelligence and reported cyber incidents to all Albert sensors to assist in identification of known malicious and anomalous activity.
- If an Albert sensor detects a match to a known threat signature in network traffic, an alert is sent to the CIS Security Operations Center (SOC) for analysis.
- Cybersecurity experts at the CIS SOC analyze the Albert alert and escalate to the SLTT/election community partner if it is determined to be a credible threat. Escalated alerts are communicated in an average of less than five minutes. The SLTT/election community partner can then decide how they want to handle the alert. As a passive IDS, Albert can take no responsive action against threats it detects.
Watch this video to learn more about how Albert works
What is an Intrusion Detection System?
An IDS is industry-standard technology for network defense. The National Institute of Standards and Technology (NIS) defines an Intrusion Detection System (IDS) as “a security service that monitors and analyzes network or system events for the purpose of finding, and providing real-time or near real-time warning of, attempts to access system resources in an unauthorized manner.” Also known as a network intrusion detection system (NIDS), an IDS often comes in the form of a piece of hardware, such as a computer or server, or a dedicated appliance.
An IDS sits on a network to watch for malicious or suspicious network activity that it sees. In most cases, it performs this monitoring by utilizing signatures, or pre-defined patterns determined to be malicious. If network traffic matches the pattern, the IDS generates an alert.
An IDS is different from an intrusion prevention system (IPS). The latter can stop traffic; it’s “active.” Meanwhile, an IDS cannot interfere with network activity; it’s “passive.” It’s therefore imperative that whoever receives the alert takes action in some way.
Is Albert effective?
Albert sensors, in combination with a layered “defense in depth” approach to cybersecurity, have proven to be highly effective in protecting against cyber threats, including known ransomware. While no IDS can detect 100% of malicious traffic, this powerful capability detects virtually all known threats that have documented IDS signatures.
As a signature-based IDS, Albert is as effective as the signatures with which it is configured. CIS subscribes to the latest commercially-available signature sets, subsequently deploying those signature sets to Albert. CIS works diligently to also research and develop custom signatures to deploy to Albert that are specifically tuned to the threats that may impact U.S. SLTT government and election community organizations.
Another factor leading to Albert’s effectiveness is the speed at which the 24x7x365 CIS Security Operations Center (SOC) reviews and notifies monitored organizations of threats the Albert sensor detects. The CIS SOC notifies the monitored organization with an industry-leading average of less than five minutes when the Albert sensor alerts on potential malicious or anomalous activity. This response speed enables cybersecurity defenders to quickly take action to defend their networks and contain threats to reduce the impact of a successful attack.
Albert sensors and associated SOC support are approximately one third the cost of alternative commercial products and monitoring services, and the average alert response time of under five minutes is much quicker than alternative services.
Can Albert take any action on observed network traffic?
Data & Hardware
What other data is collected?
We collect data about the traffic, not what’s in the traffic, in addition to alert data about the signatures firing. This data is called NetFlow. NetFlow is only collected for on-premises sensors and not available for Cloud.
- Source IP
- Destination IP
- Source port
- Destination port
- TCP flags
- Number of bytes of traffic sent and received
- Timestamp information (start, end, and duration of connection)
What hardware do I need?
The on-premises Albert service can be supplied as a turnkey solution or utilizes physical or virtual commodity hardware to provide a robust offering at a low cost. We recommend supplying an Albert sensor with network traffic by way of a network tap or data aggregator if your infrastructure already supports these options. For smaller <1Gb networks, a span port off a router or switch will work well. Please contact CIS Services for assistance with sizing your hardware.
What are the Albert Cloud Requirements?
Albert Cloud is not available at this time.
Who manages the sensor?
Monitoring, as well as full management of the sensor, is handled by the CIS SOC. This includes maintaining the operating system, IDS engine, NetFlow tools, and signature sets. CIS will work with your organization to make signature modifications upon request as well as collaborate to write custom signatures to detect specific types of malicious activity on your network.
What reports are provided to Albert customers?
Does Albert communicate with voting systems?
Services & Cost
What services are provided with Albert Monitoring and Management?
- 24×7 network monitoring from the CIS SOC (U.S.-based)
- Alerts about potentially malicious activity
- Monthly activity summary reports
What are my network monitoring options?
Albert can monitor on-premises networks.
How much does Network Monitoring and Management cost?
Pricing is based on average Internet connection utilization. A one-time initiation fee per sensor applies. To find out more about network security monitoring, contact us today at [email protected].
Data and Information Sharing
What information does CIS share with the federal government?
Generally, the Cybersecurity and Infrastructure Security Agency (CISA) has visibility into certain data that is derived from sensors/services that are funded via the Cooperative Agreement subject to confidentiality obligations. For example, CISA may request and receive the full set of Albert Network Monitoring and Management data only for those Albert deployments funded via the Cooperative Agreement, which represents approximately 20% of the deployed Albert sensor fleet.
Albert: Roughly 80% of deployed Albert sensors are paid for by U.S. state and local governments. For these SLTT-funded sensors, Albert alert data and Albert NetFlow metadata is shared with Federal partners only with the explicit approval of the individual hosting state or local organization.
The deployment of the remaining Albert sensors is funded by Congressional appropriation through the Multi-State and Elections Infrastructure Information Sharing and Analysis Centers (MS- and EI-ISAC) to support cyber defense across the U.S. below the federal level. For these CISA-funded sensors, information shared with federal partners is limited to Albert alert data and Albert NetFlow metadata.
NCSR: For the Nationwide Cybersecurity Review (NCSR), CISA currently sees only anonymized data, such as threat data and self-reported maturity scores by sector. To date, this data is anonymized, so there is no organization-specific information included.
Cyber Incident Response: For cyber incident response cases, CIS shares information with CISA, including affected entity name, type of case, and case notes, unless the organization explicitly instructs the MS-ISAC not to do so. An organization may mark their case as TLP Red, in which case only non-attributional information will be shared with CISA.
Albert NetFlow Extract Tool (ANET)
What are the requirements for an organization to access ANET?
- The organization must have at least one sensor. The Albert sensor NetFlow queries will also include network activity across all sub sensors associated with the Albert device the contracting account has in production
- The organization and user must have CIS Portal access
- Those who receive Albert alert notification emails from the CIS Security Operations Center will have access to ANET.
How do I access the ANET tool?
Log into the CIS Portal and navigate to My Organization > Manage Products, Services and Resources.
Once on this page, you will see a tile labeled “Albert NetFlow Extract Tool.” Click the “Launch Application” button to open the tool in a new web browser tab.
Note: If you do not see the tile, please reach out to the CIS support team for assistance.
How do query credits work?
Organizations receive 32 query credits per month included in their baseline Albert package. Credits are consumed based on the type of query the user runs. Complex queries may take as many as 8 credits.
Query credits will be automatically refilled monthly to the 32 credit level. The provided credits do not rollover month-to-month or accrue.
If I've used all my credits how do I request more?
Additional query credits will be available for purchase for all Albert customers. Please contact the CIS support team for assistance. If additional query credits are purchased, these credits will rollover.
Can I query data which falls out of the date range or query type supported by ANET?
There are pre-defined queries which may be selected for a 7-day date range within the past 30 days.
- DNS Activity - retrieves Albert / DNS activity, within the dates referenced, for a specific domain
- Inbound Activity – retrieves only inbound Albert activity, within the dates referenced, from a specific IP address
- IP Activity – retrieves all Albert activity, within the dates referenced, to and from a specific IP address
For queries outside of the scope described above, please contact the CIS SOC team at [email protected].