White Papers
Download guides, security framework mappings, and other documents
Filter
258 Results Found
Solutions
211 - 220 of 258 results
Published on 09.18.2018
Malicious actors leverage public interest during natural disasters and other high profile events in order to conduct financial fraud and dissemin...
Published on 09.10.2018
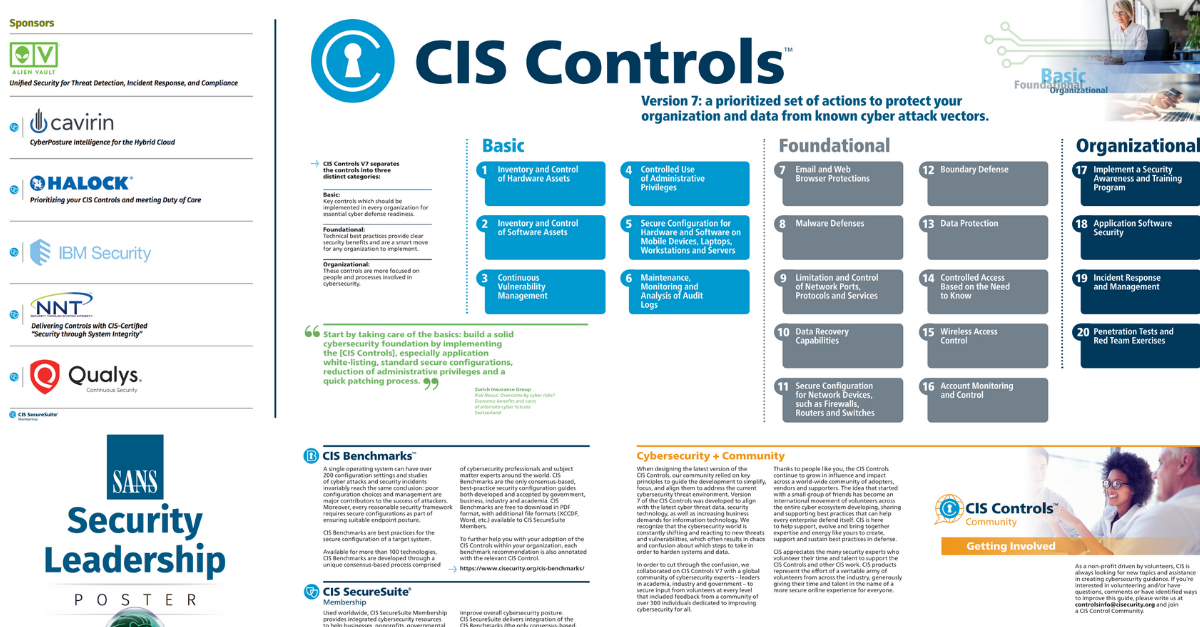
CIS Controls V7 is a prioritized set of actions to protect your organization and data from known cyber attack vectors. Learn about the basic, fou...
Published on 09.05.2018
A quick desk reference for State, Local, Tribal, and Territorial governments
Published on 07.31.2018
Overview Spear phishing occurs when cyber threat actors send a targeted electronic communication to an individual or a small group of users, whil...
Published on 07.06.2018
Learn how CIS continued to experience growth and expand recognition as a global leader in cybersecurity throughout 2017
Published on 06.21.2018
By walking through CIS Controls Version 7 with this Companion document, the reader should be able to tailor the CIS Controls in the context of a ...
Published on 05.09.2018
Learn how the following steps can help organizations deal with a cyber incident. Establish Reliable Facts and a Way to Stay Informed Mobilize a R...
Published on 04.23.2018
Overview The impact of publicly exposed user credentials has far reaching affects, because credential reuse can result in data breaches, system c...
Published on 03.19.2018
Measures & Metrics for CIS Controls V7
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More