Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
80 Results Found
Solutions
Industry
41 - 50 of 80 results
Published on 01.15.2021
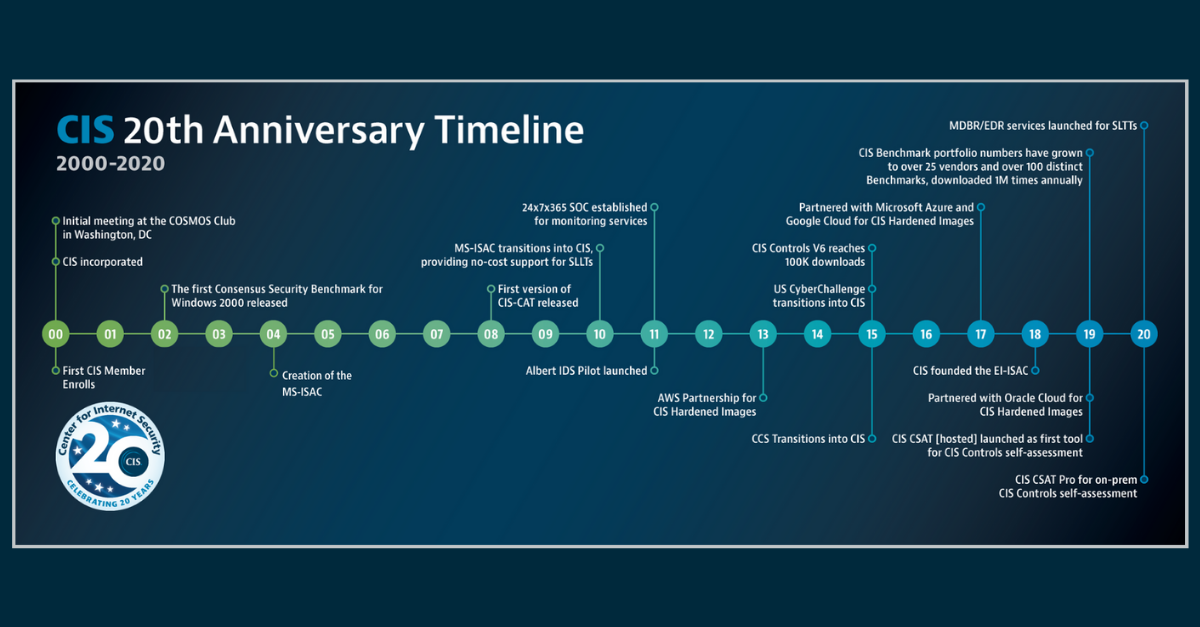
In 2020, the Center for Internet Security (CIS) recently celebrated its 20thyear of creating confidence in the connected world. In preparation fo...
CIS Hardened ImagesCIS BenchmarksCIS ControlsCIS CyberMarketCIS Services
Published on 12.17.2020
Organizations with cloud workloads need to protect themselves against a variety of risks. While most organizations focus on security against hack...
CIS Hardened Images
Published on 12.01.2020
Securing your IT infrastructure can be a challenge, especially if you’re working in a regulated environment. To help organizations with this chal...
CIS Hardened ImagesCIS Benchmarks
Published on 11.24.2020
Cloud service providers (CSPs) have changed the way organizations of all sizes architect and deploy their IT environments. CSPs now make it possi...
CIS Hardened ImagesCIS Benchmarks
Published on 11.23.2020
This year, the Center for Internet Security (CIS) is celebrating 20 years of making the connected world a safer place for people, businesses, and...
CIS Hardened ImagesCIS BenchmarksCIS ControlsCIS ServicesCIS SecureSuite
Published on 11.17.2020
CIS continues to bring security to the cloud with virtual machine images pre-configured to the recommendations of the CIS Benchmarks. There are m...
CIS Hardened Images
Published on 11.05.2020
Increased demand for remote work capabilities continues throughout 2020. Customer security in the cloud remains an important part of that growth....
CIS Hardened ImagesCIS Benchmarks
Published on 09.02.2020
Oracle Cloud users have a new resource to help secure their cloud environments: the CIS Oracle Cloud Infrastructure Foundations Benchmark. This o...
CIS Hardened ImagesCIS Benchmarks
Published on 08.13.2020
The shift to a global remote workforce is demonstrating just how difficult securing a cloud environment can be. This is especially true for organ...
CIS Hardened Images
Published on 06.09.2020
The COVID-19 pandemic changed business practices worldwide. The traditional workplace transformed; for many, the “new norm” is now a home office ...
CIS Hardened Images
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More