Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
80 Results Found
Solutions
Industry
21 - 30 of 80 results
Published on 11.04.2021
This year, Amazon Web Services (AWS) returns to hosting its cloud computing conference, AWS re:Invent 2021, in person. Cloud professionals from a...
CIS Hardened ImagesCIS Benchmarks
Published on 10.21.2021
Just under 25% of the internet’s busiest websites – including Dropbox, Netflix, and WordPress.com – served or proxied NGNIX in July 2021, accordi...
CIS Hardened ImagesCIS Benchmarks
Published on 10.06.2021
It’s obvious that the remote capabilities of the modern day office have transformed permanently. Most organizations will see an increase in hybri...
CIS Hardened ImagesCIS Benchmarks
Published on 09.23.2021
Cybercriminals target public sector organizations every day. From ransomware attacks to data theft, systems need defense-in-depth best practices ...
CIS Hardened ImagesCIS Benchmarks
Published on 09.09.2021
The Center for Internet Security (CIS) is excited to sponsor and attend the Amazon Web Services (AWS) Public Sector Summit at booth 209. This yea...
CIS Hardened ImagesCIS Benchmarks
Published on 09.07.2021
Ensuring your organization’s IT environment is not only secure, but also patched regularly, can be challenging. Migrating to the cloud can help a...
CIS Hardened ImagesCIS Benchmarks
Published on 08.18.2021
As organizations utilizing the cloud mature, they find more innovative and effective solutions for their workloads. Containerized applications of...
CIS Hardened ImagesCIS Benchmarks
Published on 08.12.2021
Organizations tasked with meeting regulatory framework compliance know the difficulties they will face. On top of the resource hours, it can be c...
CIS Hardened ImagesCIS Benchmarks
Published on 07.08.2021
The Center for Internet Security (CIS) has released three new CIS Hardened Images. CIS built two of these new hardened virtual machines (VMs) on ...
CIS Hardened ImagesCIS Benchmarks
Published on 06.21.2021
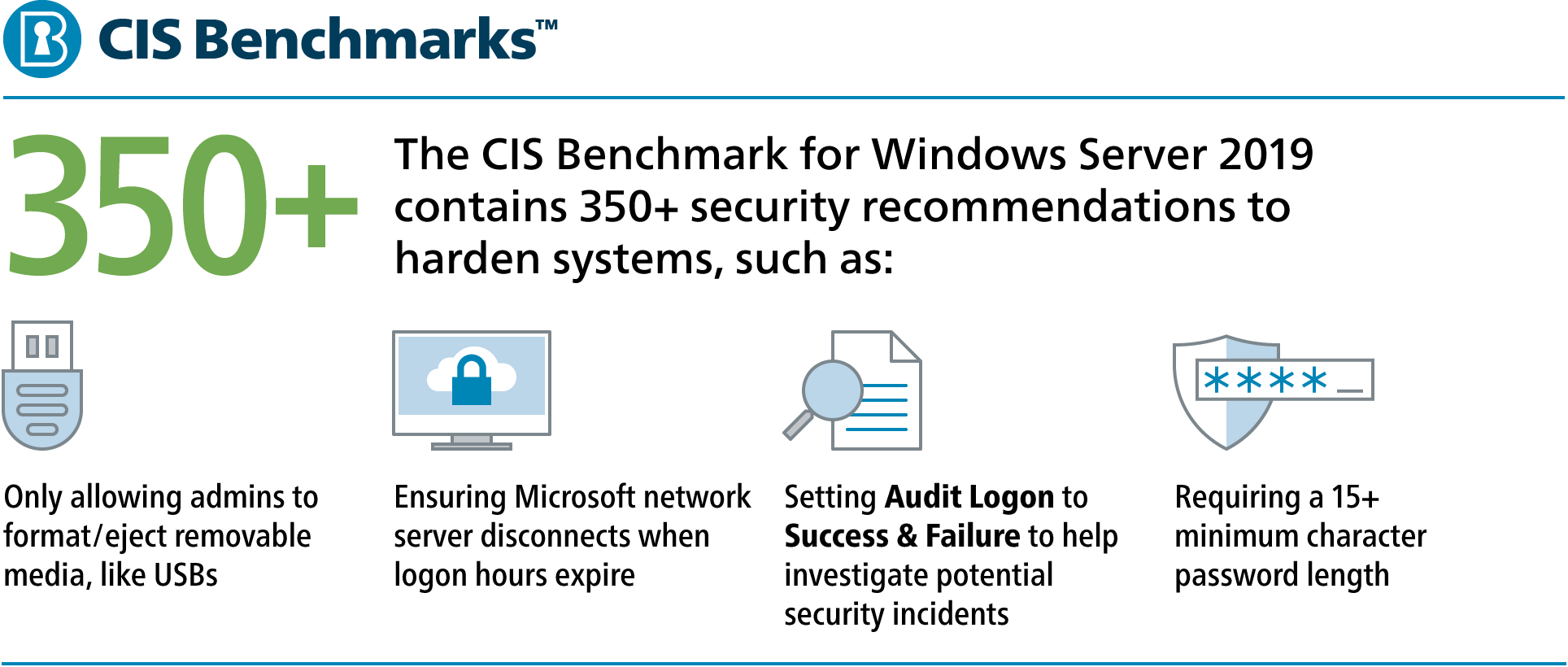
Cloud security is just as vital as on-premises security. Hundreds of security recommendations may exist to harden your Operating Systems (OS). Th...
CIS Hardened ImagesCIS BenchmarksCIS SecureSuite
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More