Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
633 Results Found
Solutions
Industry
271 - 280 of 633 results
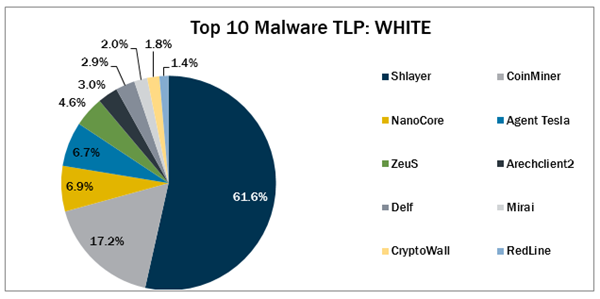
Published on 04.15.2022
In March 2022, the Top 10 stayed consistent with the previous month with malware changing spots in the Top 10.
Published on 04.14.2022
Many SLTTs have been grappling with the same five cybersecurity concerns since 2015. But these obstacles aren't insurmountable.
CIS Services
Published on 04.12.2022
Asset visibility requires understanding which types of devices exist in your environments and what they mean to your security program.
CIS Controls
Published on 04.07.2022
The CIS Benchmarks development team has been hard at work preparing several brand new Benchmarks and updates for April 2022.
CIS BenchmarksTechnology
Published on 04.01.2022
CIS and the MS-ISAC shares how U.S. state and local governments can defend themselves against Russian cyber-attacks.
MS-ISAC
Published on 03.28.2022
Making security simpler as controls become integrated into organizations' zero-trust journeys is a tremendous opportunity for democratizing secur...
Published on 03.25.2022
The CIS Critical Security Controls (CIS Controls) team has created guide to help organizations create secure cloud environments.
CIS Controls
Published on 03.22.2022
A new CIS Benchmark was created to offer added protection for election management system gateway machines.
CIS Benchmarks
Published on 03.17.2022
CIS's SOC 2 Type II compliance ensures members’ data and associated information is protected at all times with all compliance requirements.
CIS Controls
Published on 03.15.2022
In February 2022, Arechlient2, CryptoWall, and Delf. CryptoWall returned to the Top 10, while Arechclient2 and Delf made their first appearances.
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More




.png?h=313&iar=0&w=600&rev=7206e533fcb94f09ab8c6137aa0a770e&hash=E8A74A375604DD2C5C9EA7BBBCF6DBE9)