Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
586 Results Found
251 - 260 of 586 results
Published on 12.02.2021
Hear from the Experts with these Cybersecurity PodcastsThe selection of podcasts – on everything from gaming to movies to sports – has exploded in recent years. Whatever topic you’re interested in, ch...
Published on 12.02.2021
Preventing the Most Common Cyber-Attacks with Cybersecurity TrainingMany offices are operating with a hybrid of remote and in-person workspaces as the COVID-19 pandemic continues and evolves. Wherever your team is...
Published on 12.01.2021
Why OAuth is so Important: An Interview with Justin RicherThis is the third article in this series by Kathleen Moriarty, CIS Chief Technology Officer. In this article, Moriarty interviews Justin Richer, ...
Published on 11.30.2021
Microsoft Azure Security Benchmark v3 is now mapped to CIS Critical Security Controls v8We are pleased to announce the release of the Azure Security Benchmark (ASB) v3 with mappings to the CIS Critical Security Controls (CIS Controls...
Published on 11.24.2021
Authentication and Authorization Using Single Sign-OnBy: Kathleen M. Moriarty, CIS Chief Technology Officer In order to prevent credential theft from phishing attacks, there is a push for multi-fact...
Published on 11.23.2021
End of Life Update: CIS-CAT Pro Assessor v3CIS-CAT Pro is a tool used to evaluate the cybersecurity posture of a system against the recommended policy settings outlined in the CIS Benchmar...
Published on 11.17.2021
How to Meet the Shared Responsibility Model with CISIn 2020, the shift to a global remote workforce demonstrated just how difficult securing a cloud environment can be. Now organizations face the c...
Published on 11.15.2021
For Data Compliance, Automation is KeyIn this edition of Cybersecurity Where You Are, CIS Senior VP and Chief Evangelist, Tony Sager welcomes Thordis Thorsteins, Senior Data Scientist...
Published on 11.10.2021
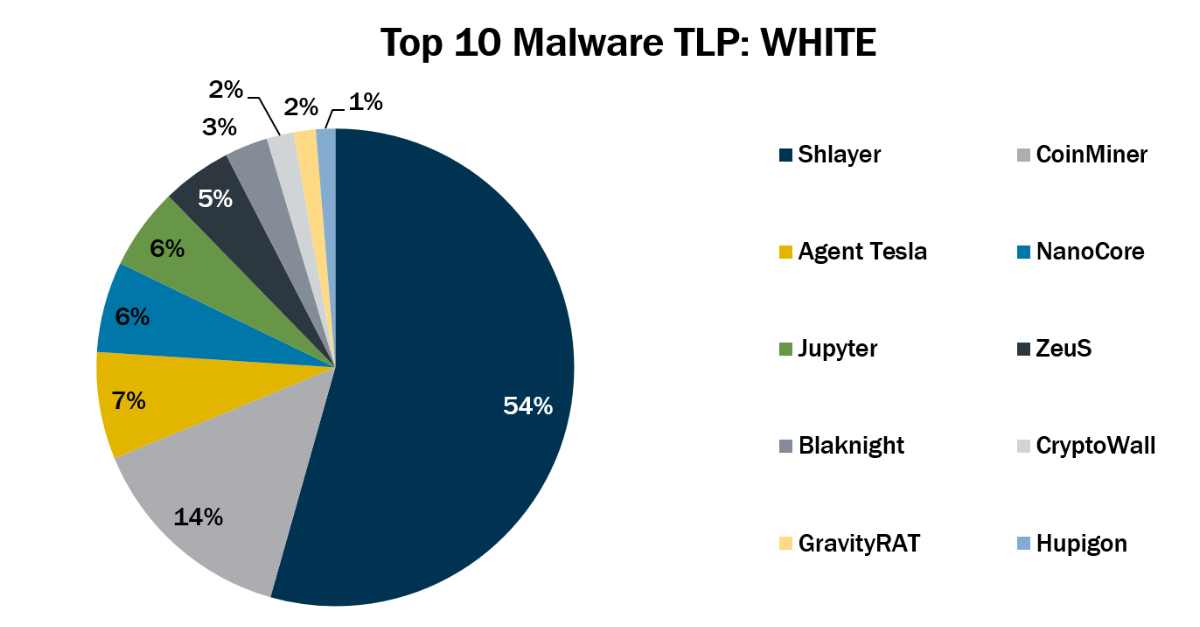
Top 10 Malware October 2021In October 2021, the Top 10 stayed consistent with the previous month with the exception of GravityRAT which made its first appearance in the Top...
Published on 11.08.2021
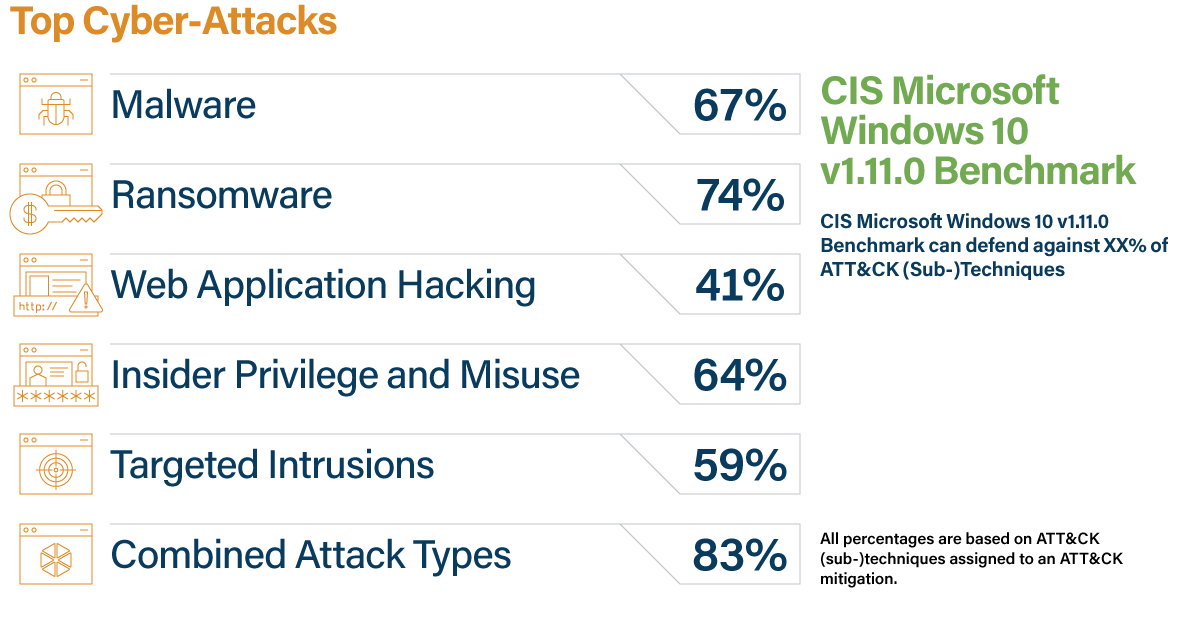
Cyber-Attack Defense: CIS Benchmarks + CDM + MITRE ATT&CKBy Jennifer Jarose, CIS Cybersecurity Engineer, CIS Benchmarks Six trillion dollars…that’s the amount global cybercrime is expected to cost this ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More