Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter
596 Results Found
Solutions
Industry
511 - 520 of 596 results
Published on 10.22.2018
By Sean Atkinson, Chief Information Security Officer The Department of Homeland Security (DHS) has defined 16 critical infrastructure sectors in ...
CIS Controls
Published on 10.18.2018
In an effort to be fully prepared for a cyber incident, it’s important for key members in an organization to know the proper steps to take when h...
MS-ISAC
Published on 10.16.2018
CIS SecureSuite® Members can now customize CIS Benchmarks™ within the CIS WorkBench platform. This added flexibility will help users tailor secur...
CIS SecureSuite
Published on 10.15.2018
The CIS Controls are a prioritized set of actions that collectively form a defense-in-depth set of cybersecurity best practices. Together, they m...
CIS Controls
Published on 10.11.2018
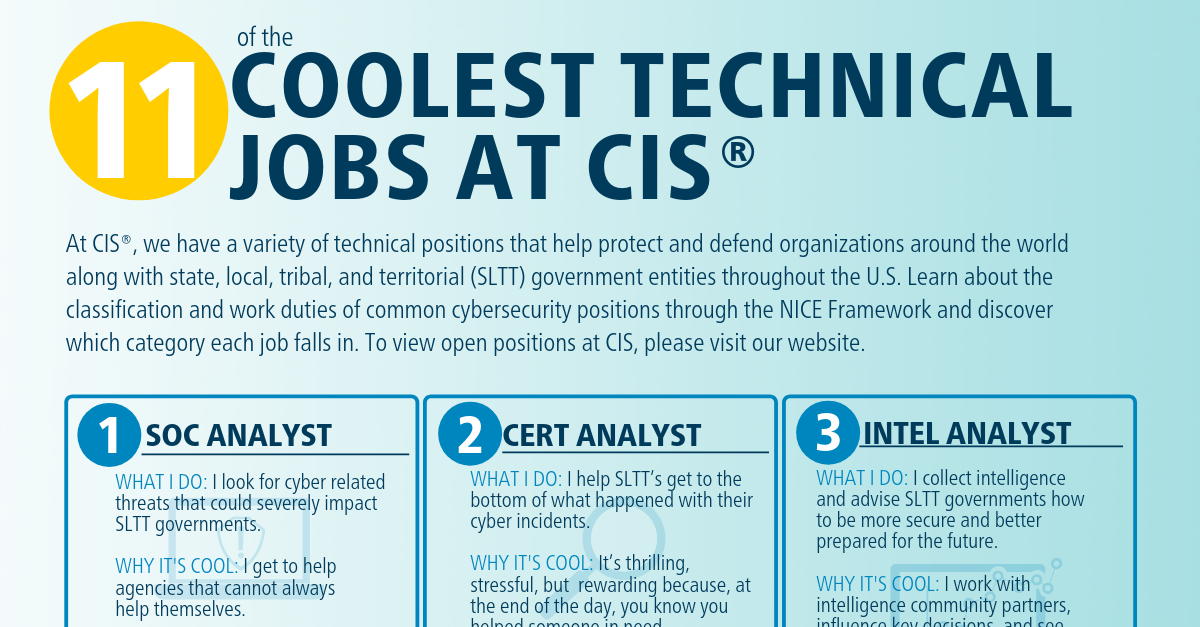
There are hundreds of different technical jobs in the cybersecurity industry, with millions of unfilled positions around the globe. Each position...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Published on 10.09.2018
To celebrate this week’s theme of ‘Educating for a Career in Cybersecurity’ during Cybersecurity Awareness Month (CSAM), we wanted to get an insi...
CIS BenchmarksCIS ControlsCIS CyberMarketCIS Hardened ImagesCIS Services
Published on 10.04.2018
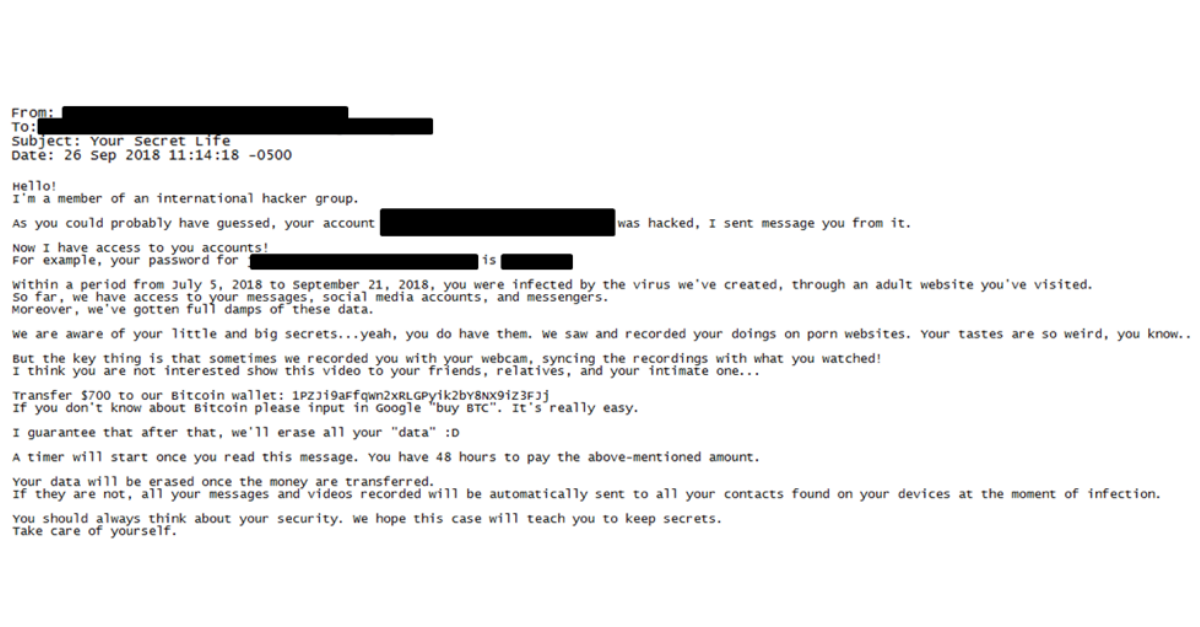
Sextortion hoax scams continue to affect state, local, tribal, and territorial (SLTT) government employees, who are reporting updated email tacti...
MS-ISAC
Published on 10.02.2018
Facing everything from viruses to malware, home and personal networks can be just as vulnerable to cyber crime as organizational systems. We spok...
CIS Controls
Published on 09.27.2018
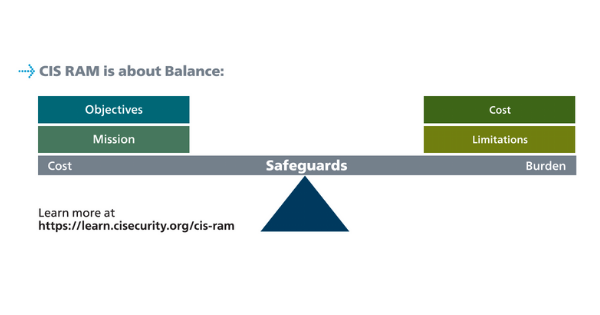
Want to know more about risk analysis? Check out the presentation below by Chris Cronin, a partner at Halock Security Labs and Chair of the DoCRA...
CIS Controls
Published on 09.25.2018
More than 9,000 members of the CIS Benchmarks™ Community have developed and updated CIS Benchmarks for over 150 technologies. Our latest communit...
CIS BenchmarksTechnology
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More