Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
582 Results Found
381 - 390 of 582 results
Published on 09.21.2020
Protecting Organizations From Today’s Top Cyber ThreatsCyber threats are constantly evolving. As recently as 2016, Trojan malware accounted for nearly 50% of all breaches. Today, they are responsible ...
Published on 09.17.2020
Business Email Compromise: Cosmic LynxBusiness Email Compromise Business Email Compromise (BEC), sometimes known as Email Account Compromise (EAC), is a common scam that leverages soc...
Published on 09.15.2020
The Journey to Better Cybersecurity in 2020 and BeyondThe year 2020 will be remembered as the time when widespread internet-enabled remote working became a reality. IT administrators saw their respon...
Published on 09.14.2020
CIS Benchmarks September 2020 UpdateCIS Amazon Web Services Foundations Benchmark v1.3.0 Prescriptive guidance for configuring security options for a subset of Amazon Web Services (...
Published on 09.02.2020
New CIS Foundations Benchmark for Oracle CloudOracle Cloud users have a new resource to help secure their cloud environments: the CIS Oracle Cloud Infrastructure Foundations Benchmark. This o...
Published on 09.02.2020
Malicious Domain Blocking and Reporting (MDBR) Newest Service for U.S. SLTTsMalicious Domain Blocking and Reporting (MDBR) is the latest service that the Multi-State Information Sharing and Analysis Center (MS-ISAC) and E...
Published on 08.21.2020
CIS Benchmarks August 2020 UpdateCIS Password Policy Guide The CIS Benchmarks Community has created a new CIS Password Policy Guide, with up-to-date best practices for creating p...
Published on 08.20.2020
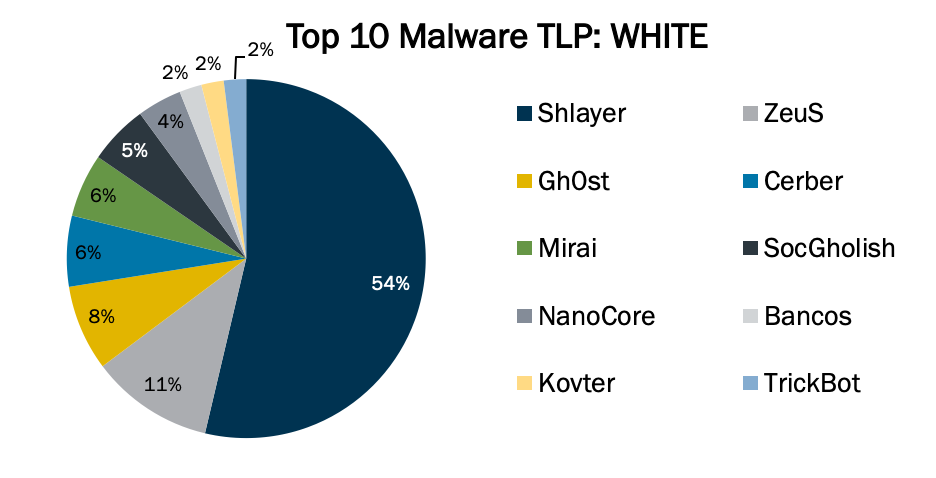
Top 10 Malware July 2020Top 10 Malware composition was consistent through July 2020, with the exception of Shlayer, Bancos, and TrickBot. The Top 10 Malware variants com...
Published on 08.18.2020
Improve Your Organization’s Cyber Hygiene with CIS CSAT ProBasic cyber hygiene is the foundation for any good cybersecurity program. Tony Sager, CIS VP and Chief Evangelist, recently defined basic cyber h...
Published on 08.13.2020
How to Provide a Secure Cloud Environment for Remote WorkersThe shift to a global remote workforce is demonstrating just how difficult securing a cloud environment can be. This is especially true for organ...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More