Blog Posts
Industry news, product updates, videos, infographics, and more from CIS
Filter by Topic
582 Results Found
241 - 250 of 582 results
Published on 01.04.2022
New Hardened macOS 11 & 10.15 VMs in AWS MarketplaceApple users rejoice! CIS Hardened Images for macOS Big Sur (11) and Catalina (10.15) are now available in Amazon Web Services (AWS) Marketplace. ...
Published on 01.03.2022
NSA Guidance: Zero Trust Applied to 5G Cloud Infrastructure contd: Parts 3 and 4Part 2 of a 2-part series By: Kathleen M. Moriarty, CIS Chief Technology Officer and active participant in the Critical Infrastructure Partnershi...
Published on 12.15.2021
How to Defend Against Windows Management Instrumentation AttacksThe Windows Management Instrumentation (WMI) protocol – infrastructure on a Windows-based operating system – is used for management data and oper...
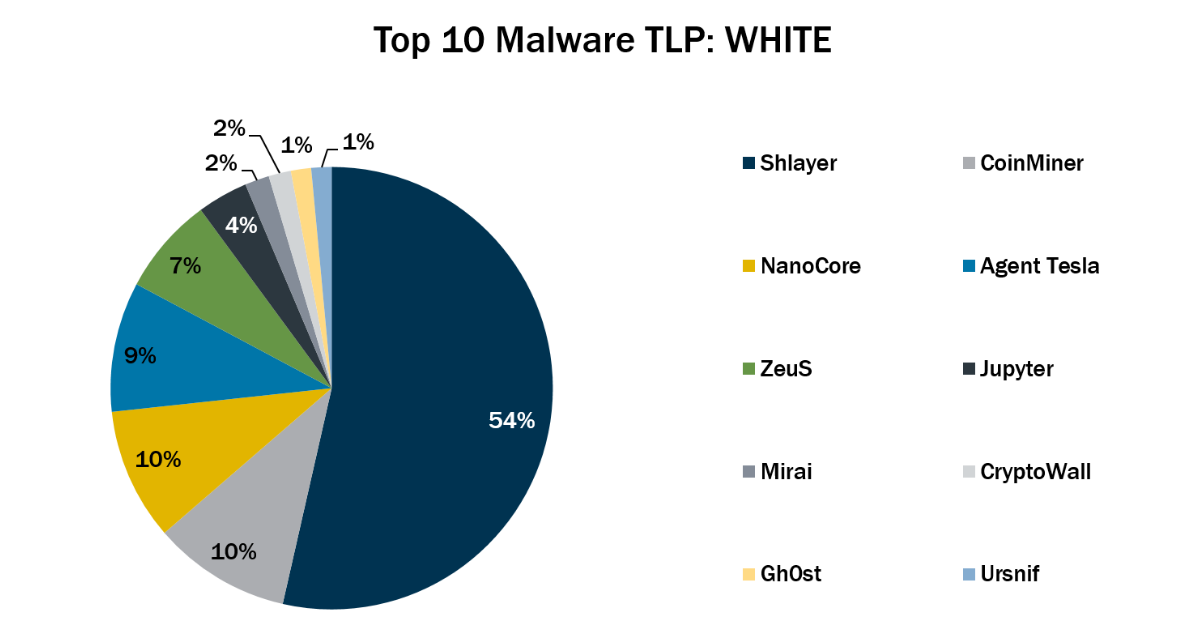
Published on 12.12.2021
Top 10 Malware November 2021In November 2021, the Top 10 stayed consistent with the previous month with the exception of Gh0st, Mirai, and Ursnif, which returned to the Top ...
Published on 12.09.2021
CIS Benchmarks December 2021 UpdateThe following CIS Benchmarks have been updated or released. We’ve highlighted the major updates below. Each Benchmark includes a full changelog ...
Published on 12.07.2021
NSA Guidance: Zero Trust Applied to 5G Cloud Infrastructure: Parts 1 and 2Part 1 of a 2-part series By: Kathleen M. Moriarty, CIS Chief Technology Officer and active participant in the Critical Infrastructure Partnershi...
Published on 12.02.2021
Hear from the Experts with these Cybersecurity PodcastsThe selection of podcasts – on everything from gaming to movies to sports – has exploded in recent years. Whatever topic you’re interested in, ch...
Published on 12.02.2021
Preventing the Most Common Cyber-Attacks with Cybersecurity TrainingMany offices are operating with a hybrid of remote and in-person workspaces as the COVID-19 pandemic continues and evolves. Wherever your team is...
Published on 12.01.2021
Why OAuth is so Important: An Interview with Justin RicherThis is the third article in this series by Kathleen Moriarty, CIS Chief Technology Officer. In this article, Moriarty interviews Justin Richer, ...
Published on 11.30.2021
Microsoft Azure Security Benchmark v3 is now mapped to CIS Critical Security Controls v8We are pleased to announce the release of the Azure Security Benchmark (ASB) v3 with mappings to the CIS Critical Security Controls (CIS Controls...
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More