All Insights
Explore security resources, trends and updates, media, podcast episodes, and more
Filter by Topic
1152 Results Found
991 - 1000 of 1152 results
Published on 08.30.2018
CIS-CAT Pro Dashboard 1.1.3. Update – What You Need to KnowThis week, CIS SecureSuite® Members are receiving an update to CIS-CAT Pro Dashboard. CIS-CAT Pro Dashboard is the companion tool to CIS-CAT Pro ...
Published on 08.28.2018
Cumulonimbus Clouds Drift…Your Cloud Configuration Shouldn’tDrifting is all good and well for the clouds in the sky, but when it comes to cloud computing, users should look out for configuration drift. A f...
Published on 08.21.2018
CommunityForce Uses CIS Hardened Images for its CustomersCIS Hardened Images are helping one software and technology firm deliver cloud-based process management solutions to over 300 organizations world...
Published on 08.21.2018
How to Manage a Multi-faceted IT EnvironmentBy Sean Atkinson, Chief Information Security Officer It has become a common practice to combine management of different technologies into a singl...
Published on 08.20.2018
Election Security Spotlight – Black, Gray, & White Hat HackersWhat it is The term “hacking” is most commonly used in reference to illegal, malicious, or illicit cyber activity. However, within the informatio...
Published on 08.15.2018
Citizens Property Insurance Corporation Adopts the CIS ControlsLearn how the CIS Controls are helping address cybersecurity in policy drafting processes.
Published on 08.09.2018
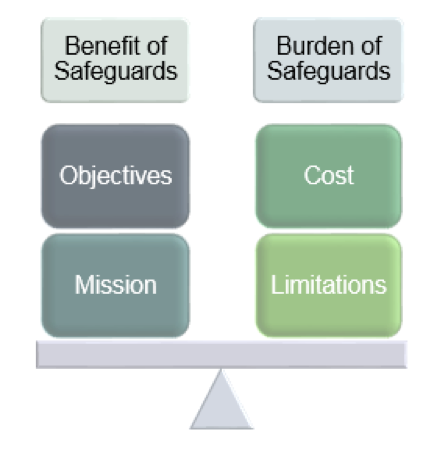
Diving Deeper into CIS RAM v1.0 FAQ – Part 2By Chris Cronin, Partner, HALOCK Security Labs CIS RAM v1.0 (Center for Internet Security Risk Assessment Method), a free tool, provides step-by-...
Published on 08.07.2018
CIS RAM v1.0 (Risk Assessment Method) FAQ – Part 1CIS released CIS RAM v1.0 (Center for Internet Security Risk Assessment Method) in April 2018. Developed by HALOCK Security Labs in partnership w...
Published on 08.06.2018
Election Security Spotlight – Social EngineeringWhat is it Social engineering is the use of deception to manipulate individuals into providing a particular response, generally for a fraudulent ...
Published on 08.03.2018
Faith-based Nonprofit Uses CIS Controls as the Baseline FrameworkLearn how one organization uses the CIS Controls for basic, effective security safeguards across a variety of business units.
Explore Related Cybersecurity Solutions

Safeguard IT systems against cyber threats with more than 100 configuration guidelines across more than 25 vendor product families.
Learn MoreProtect your organization from cyber-attacks with globally recognized CIS Controls, companion guides, and mappings.
Learn MoreCIS CyberMarket
Learn MoreCIS Hardened Images
Learn MoreCIS SecureSuite
Learn MoreCIS Services
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn MoreAccess resources for threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities.
Learn More